The content of the processing plan for verification codes can be written in English as follows:
1、Definition of Verification Codes: Explain what verification codes are and their purpose in online security and user authentication.
2、Types of Verification Codes: Describe different types of verification codes, such as SMS验证码, image-based captcha, voice verification codes, and other forms of two-factor authentication.
3、Generation of Verification Codes: Explain how verification codes are generated, including the use of algorithms and random number generators to ensure uniqueness and security.

4、Storage and Security of Verification Codes: Discuss the importance of securely storing and managing verification codes, including best practices for protecting against unauthorized access and data breaches.
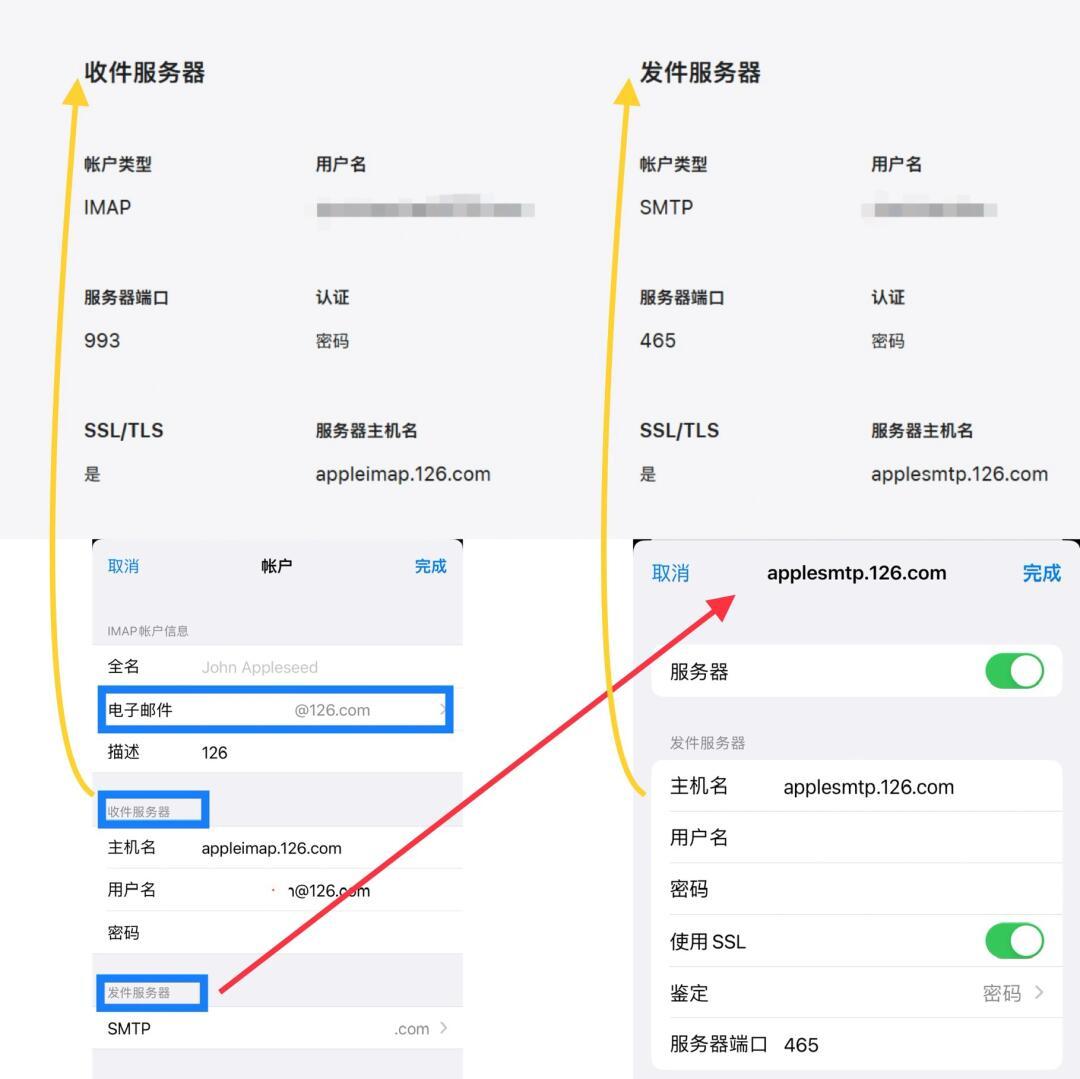
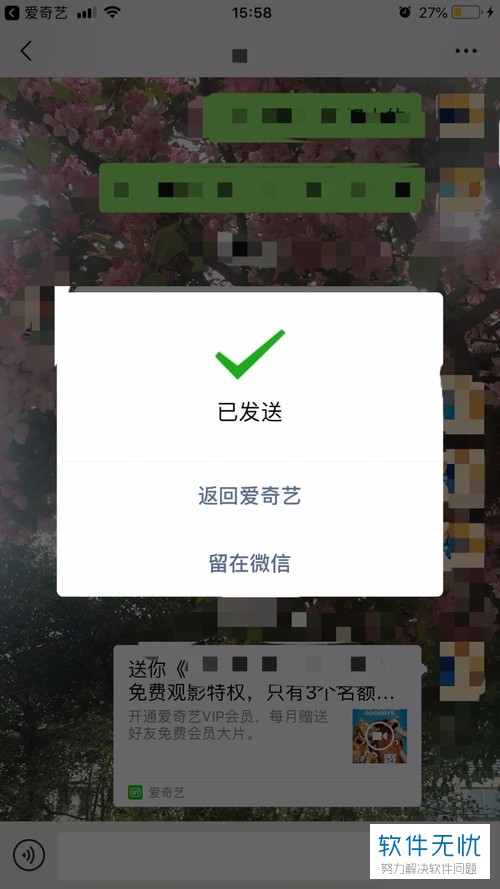
5、Verification Process: Describe the process of verifying the user’s input of the verification code, including validation techniques such as checking for code validity, expiration time, and user input accuracy.
6、Integration with Other Security Measures: Discuss how verification codes can be integrated with other security measures, such as multi-factor authentication, to enhance the security of online systems and protect against fraud and unauthorized access.
7、User Experience Considerations: Address the importance of considering user experience when implementing verification codes, including accessibility, usability, and the impact on the overall user experience.

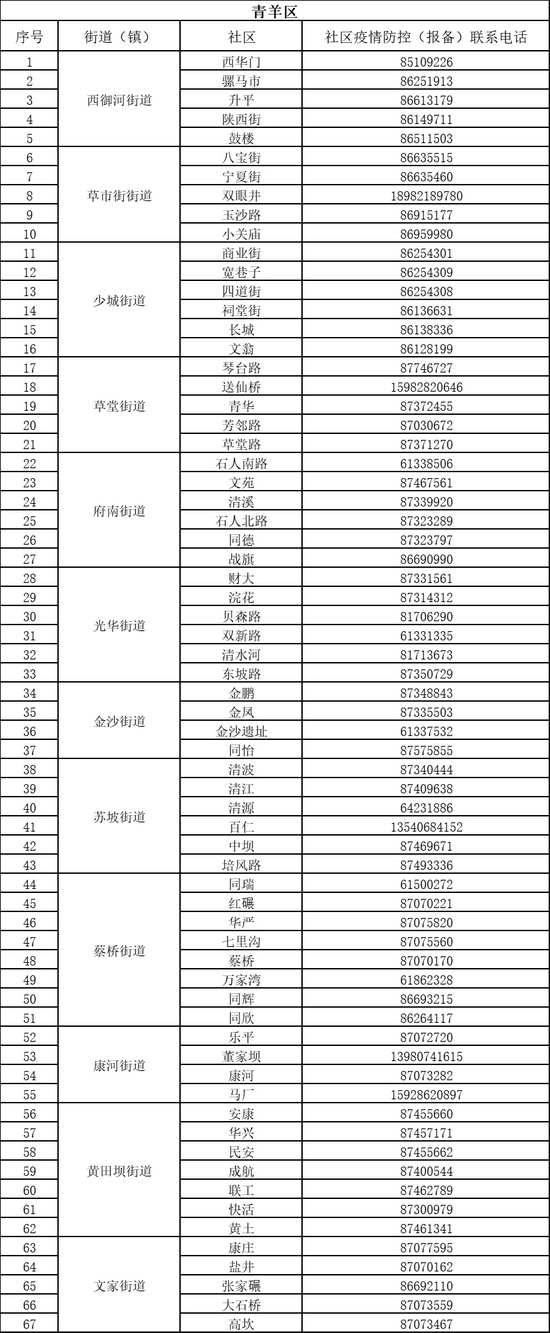
8、Compliance and Regulatory Requirements: Discuss compliance with relevant regulations and industry standards for handling sensitive data, including verification codes, to ensure adherence to privacy and security best practices.
9、Monitoring and Evaluation: Describe how to monitor and evaluate the effectiveness of verification codes in preventing unauthorized access and fraud, including regular audits and assessments of system security.
10、Conclusion: Summarize the key points of the plan and emphasize the importance of implementing secure verification code practices to protect user data and ensure system integrity.